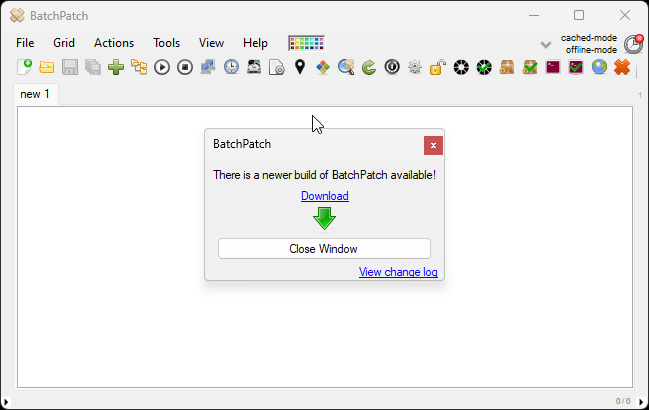
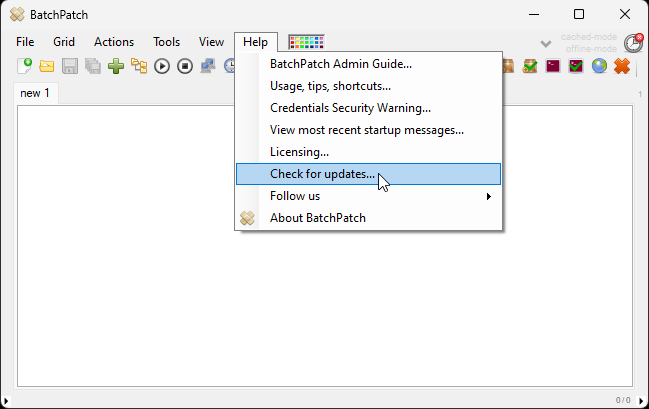
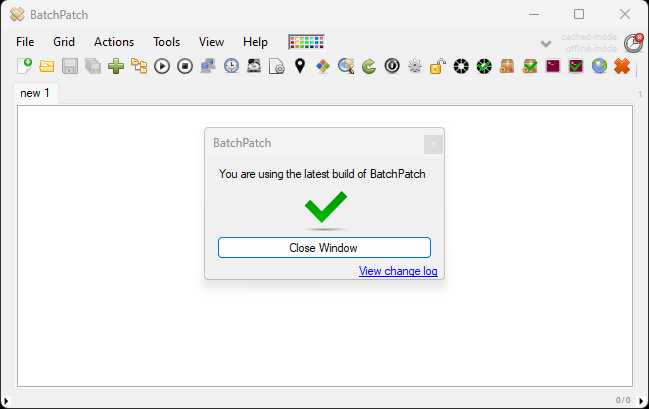
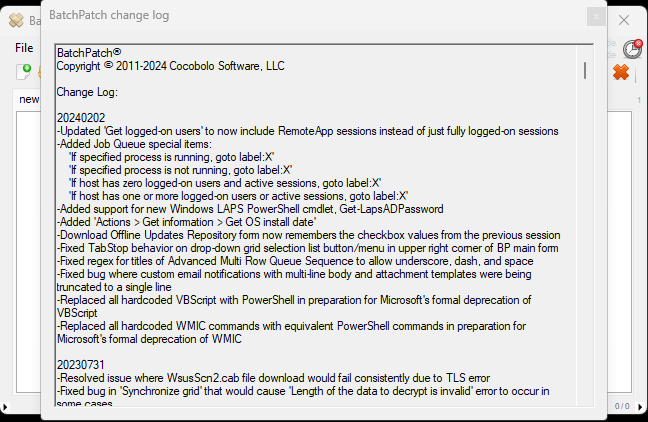
We published a new build recently. The change log is visible in the software under Help > Check for updates > View change log
-
Recent Posts
- BatchPatch Deployment Stuck Executing
- Scheduling an Email Report to be Sent for the Entire Grid
- Deploying Windows Feature Update 25H2 Remotely to Multiple Computers
- Deploying SQLServer2022-KB5063814-x64.exe with BatchPatch to Multiple Computers Simultaneously
- BatchPatch New Build Released August 2025
- Upgrading Multiple Computers from Windows 10 to Windows 11 using BatchPatch
- Deploying Office 2024 to Numerous Computers with BatchPatch
- Windows 11 Monthly Cumulative Update Fails to Install in Offline Mode: Copy To Cache: Failed. HRESULT: -2145095681 or HRESULT: -2146467818
- WSUS is Now Deprecated
- Wait for a Remote Process to Finish Running Before Installing Updates
- BatchPatch New Build Released March 2025
- BatchPatch New Build Released February 2025
- Reviewing Some of the Basic BatchPatch Functionality
- CLR error when launching BatchPatch
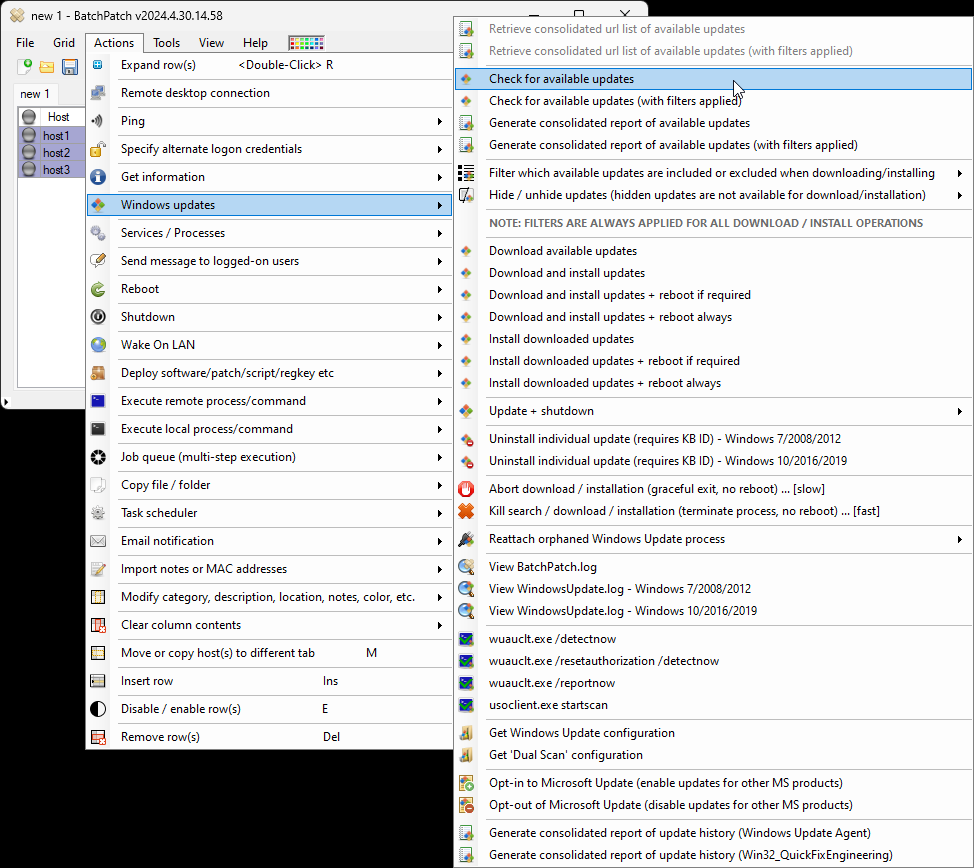
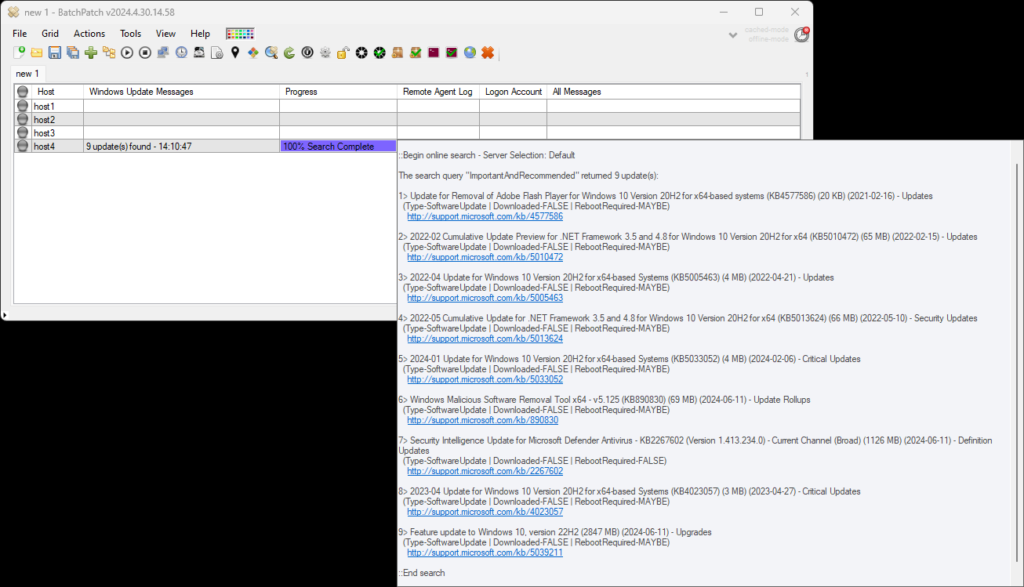
- Remotely Download and Install Windows Updates on Multiple Computers
Categories
Archives
- May 2026
- January 2026
- September 2025
- August 2025
- July 2025
- June 2025
- April 2025
- March 2025
- February 2025
- November 2024
- September 2024
- July 2024
- June 2024
- May 2024
- March 2024
- December 2023
- November 2023
- August 2023
- July 2023
- June 2023
- May 2023
- April 2023
- February 2023
- January 2023
- December 2022
- November 2022
- October 2022
- September 2022
- August 2022
- July 2022
- June 2022
- May 2022
- April 2022
- March 2022
- February 2022
- January 2022
- December 2021
- November 2021
- October 2021
- September 2021
- August 2021
- July 2021
- June 2021
- May 2021
- April 2021
- March 2021
- February 2021
- January 2021
- December 2020
- November 2020
- October 2020
- September 2020
- August 2020
- July 2020
- June 2020
- May 2020
- April 2020
- March 2020
- February 2020
- January 2020
- December 2019
- November 2019
- October 2019
- September 2019
- August 2019
- July 2019
- June 2019
- May 2019
- April 2019
- March 2019
- February 2019
- January 2019
- December 2018
- November 2018
- October 2018
- September 2018
- August 2018
- July 2018
- June 2018
- May 2018
- April 2018
- March 2018
- February 2018
- January 2018
- December 2017
- November 2017
- October 2017
- September 2017
- August 2017
- July 2017
- June 2017
- May 2017
- April 2017
- March 2017
- February 2017
- January 2017
- December 2016
- November 2016
- October 2016
- September 2016
- August 2016
- July 2016
- June 2016
- May 2016
- April 2016
- March 2016
- February 2016
- January 2016
- December 2015
- November 2015
- October 2015
- September 2015
- August 2015
- July 2015
- June 2015
- May 2015
- April 2015
- March 2015
- February 2015
- January 2015
- December 2014
- November 2014
- October 2014
- September 2014
- August 2014
- July 2014
- June 2014
- May 2014
- April 2014
- March 2014
- February 2014
- December 2013
- August 2013
- July 2013
Blogroll
RSS Links