By now most of you have surely read about the new WannaCry ransomware malware that has recently been disabling computers and networks all over the planet. Protecting your computers is very easy, but you have to care enough to make sure that you’ve done what needs to be done!
Deploying the WannaCry Patch to Current / Supported Operating Systems
In March Microsoft released a Windows update to fix the file-sharing vulnerability that WannaCry utilizes to install itself in systems. If you have been regularly installing Windows updates on your computers then you should already be safe. Make sure that you have the March updates installed, but also use this time to evaluate your entire patching policy. Do you patch semi-annually or quarterly? It is my opinion that if you are not patching every single month to apply the latest Windows updates, then you are inviting malware into your network. In 2017 if you want to keep your computers and network virus-free, the absolute number one most important and simplest thing that you should be doing is applying Windows updates relatively soon after they are released by Microsoft.
Yes, it’s true that when Microsoft releases updates they can sometimes cause problems or wreak havoc on systems, so we do *not* advocate installing Windows updates on production computers on the same day that they are released. We believe the best option 99% of the time is to wait approximately 1 week after Windows updates are released before you deploy them to all of your systems. However, you *should* deploy them to your test lab on the day they are initially released, or the day after. Then wait a week to see if you have any problems in your lab and to see if any problems are reported by other users across the internet. If any patches are determined to cause problems, do your research to make the determination whether or not you should install the patches or wait for a re-release from Microsoft.
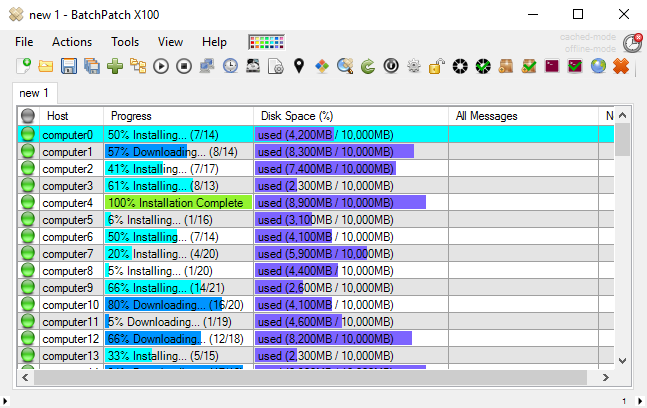
The following links demonstrate how to keep your computers up to date with BatchPatch. You may use any of these tutorials to make sure that you are protected from WannaCry:
https://batchpatch.com/using-batchpatch-to-remotely-install-windows-updates
https://batchpatch.com/remotely-install-only-a-subset-of-available-windows-updates
https://batchpatch.com/remotely-installing-windows-updates
The following link demonstrates how to see which updates have already been installed on target systems:
https://batchpatch.com/create-a-consolidated-report-of-windows-update-history
Deploying the WannaCry Patch to Unsupported / Old Operating Systems (Windows XP, Windows 2003, Windows 8)
With regard to WannaCry and older operating systems… up until a couple of days ago no patch existed for unsupported operating systems such as Windows XP, 2003, and 8. If you are still using one of these unsupported operating systems in your company, then you need to seriously consider why that’s the case. At this point in 2017 there is really almost no good reason to still be running one of these OSes, and even if you have a good reason for running one of these OSes in a corporate environment, you should still be looking to move away from them ASAP. If you’re a home user and you never got off of XP or 8, this should be a wake-up call. Your personal computer is just as vulnerable to WannaCry as any corporate machine.
If you are trying to deploy the WannaCry fix to your XP, 2003, or 8 computers, you have two options. You can use BatchPatch to apply the available Windows Updates using one of the methods outlined below in the following tutorials:
https://batchpatch.com/using-batchpatch-to-remotely-install-windows-updates
https://batchpatch.com/remotely-install-only-a-subset-of-available-windows-updates
https://batchpatch.com/remotely-installing-windows-updates
Alternatively you may deploy the standalone offline patch installer file to your target computers using the BatchPatch ‘deployment’ feature. The patch for each of the above-mentioned unsupported operating systems is linked off the bottom of this page: https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
Instructions for deploying standalone exe, msi, msu, and msp files can be found at https://batchpatch.com/software-deployment but don’t forget about the silent /quiet installation parameter! More on that here: https://batchpatch.com/understanding-and-discovering-the-silent-parameters-required-to-remotely-deploy-software-with-batchpatch